In this lab, I designed and implemented an IAM system in Okta using role-based and attribute-based access control. Automated user provisioning, enforced least privilege across AWS, GitHub, Microsoft 365. and Slack, and secured admin access with phishing-resistant MFA.
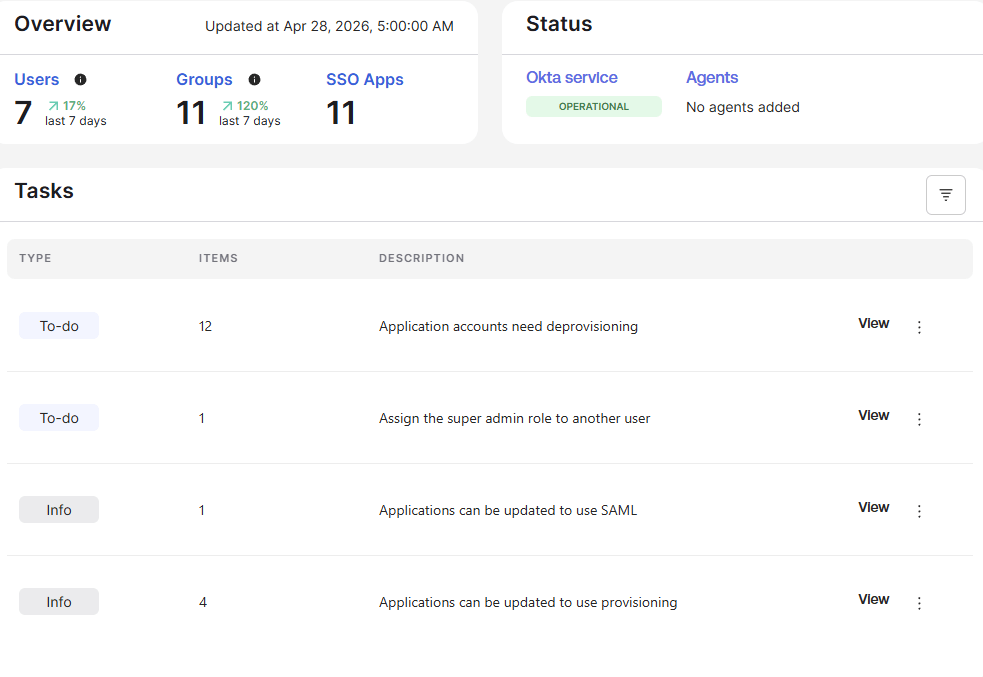
Figure 1: Admin Dashboard
Business problem
A multi-department organization required a scalable IAM solution to automate access provisioning, enforce least privilege, and secure administrative accounts.
Solution Overview
- Implemented RBAC using role-based groups
- Automated access using attribute-based group rules
- Assigned applications through dedicated access groups
- Enforced MFA with phishing-resistant authentication
- Designed restricted contractor access model
Architecture
User > Attribute > Group Rule > Role Group > App Group > Application > MFA
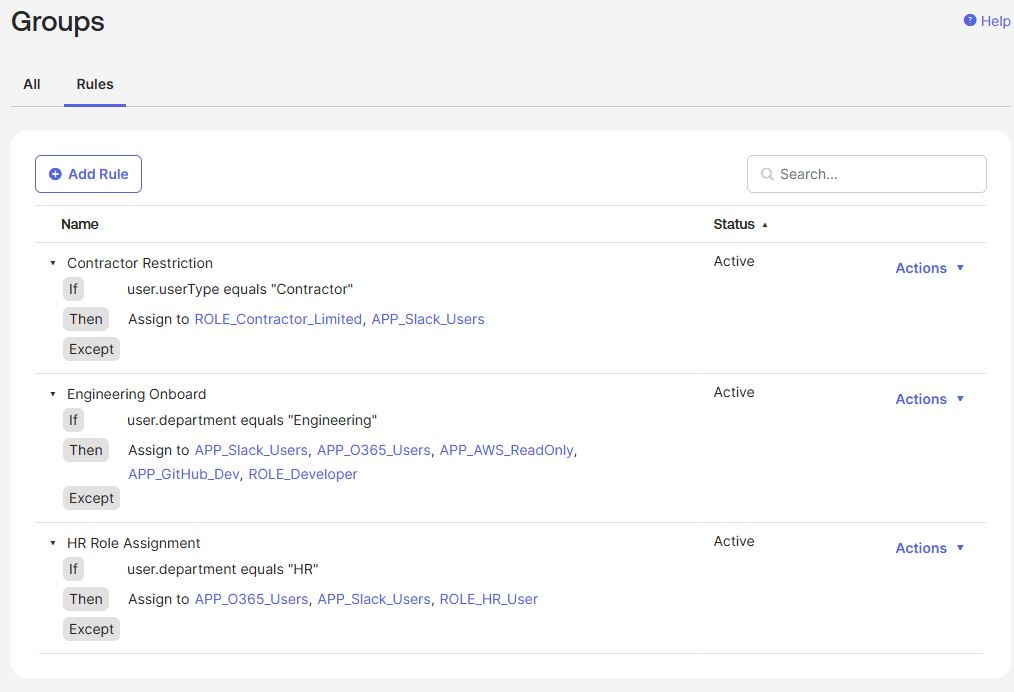
Figure 2: Group Rules
Key Features
Automated Provisioning
- Users are automatically assigned access based on department and user type
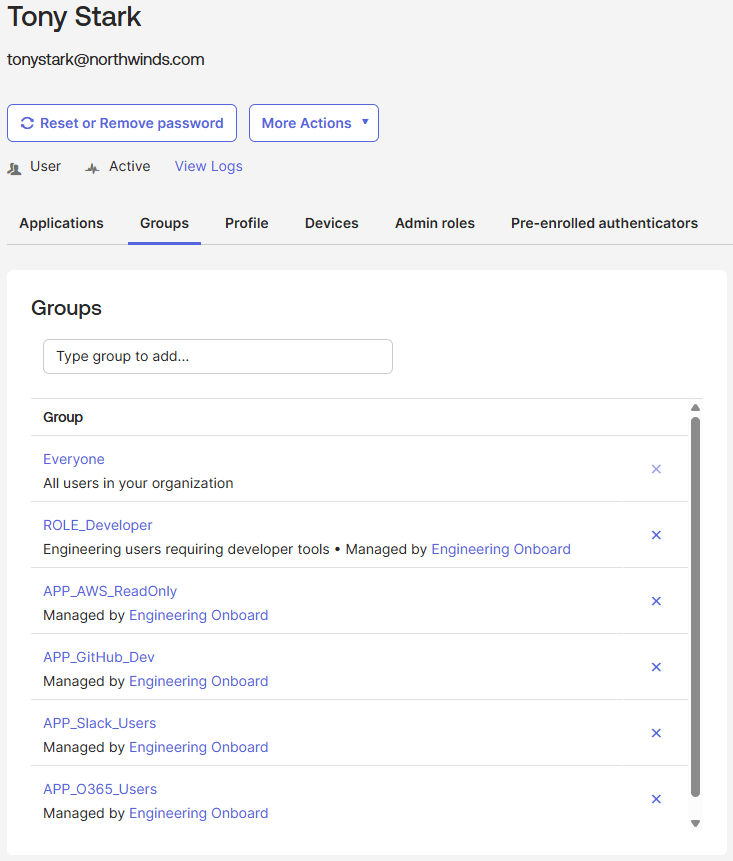
Figure 3: Automated Provisioning
Least Privilege Access
- Access is restricted based on role:
- Developers -> AWS ReadOnly + Github
- Contactors -> Slack only
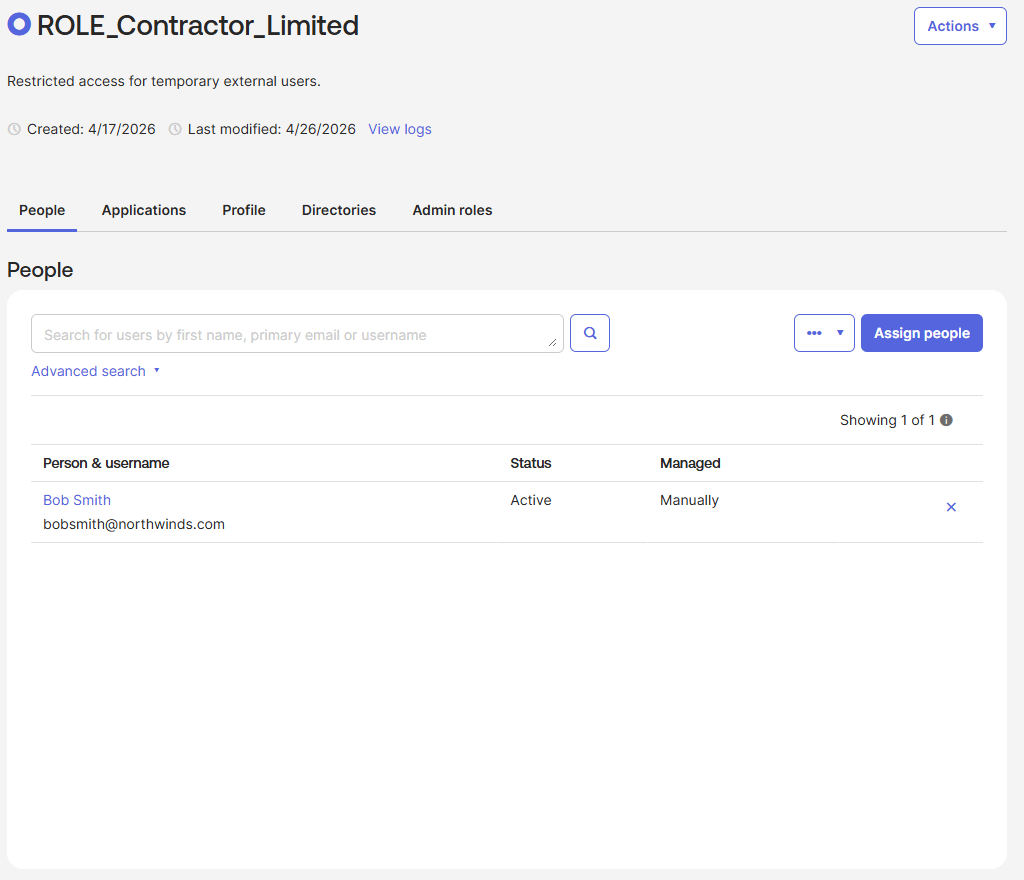
Figure 4: Contractor Role Group
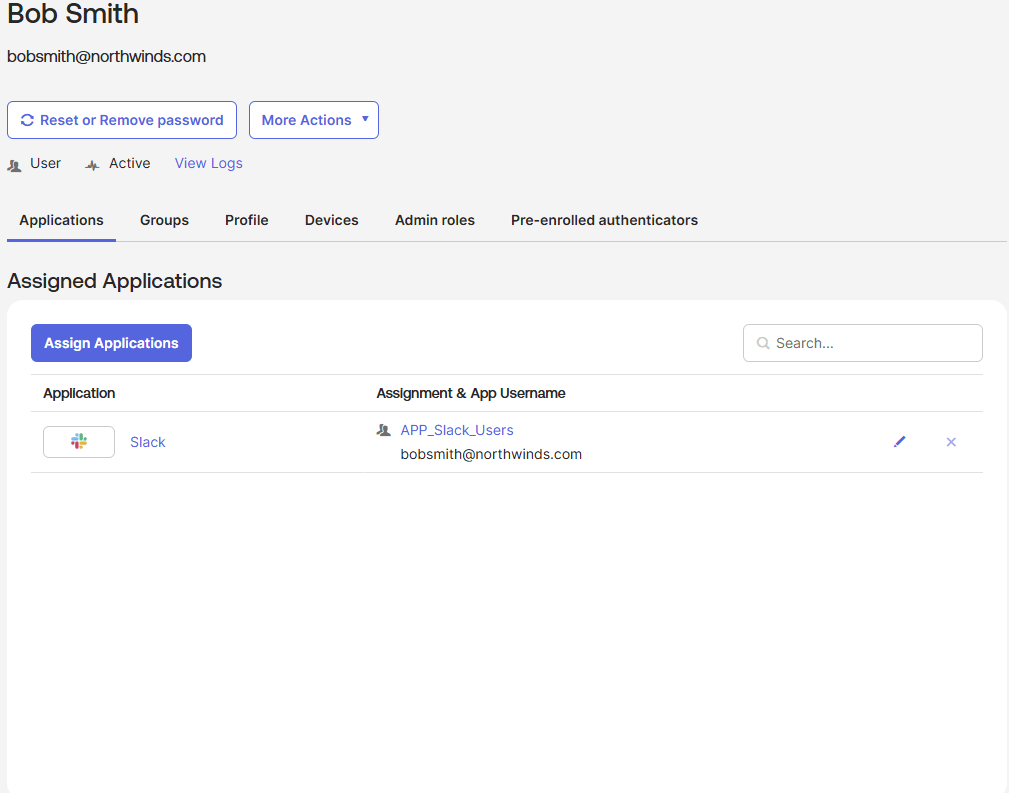
Figure 5: Contractor Assigned Application
Secure Authentication
- Admin sccess requires:
- Two-factor aunthentication
- Phishing-resistant login (Okta Verify FastPass)
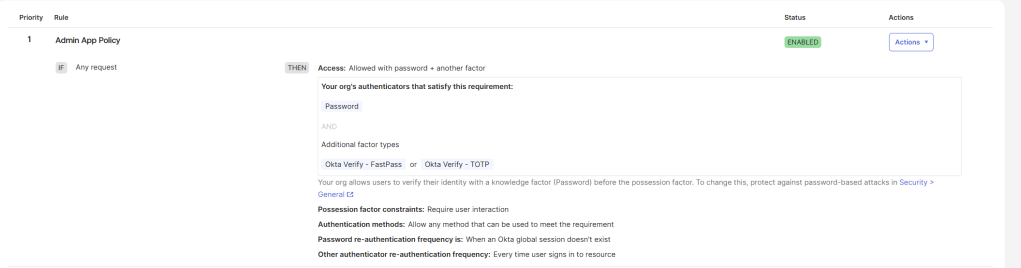
Figure 6 : MFA Policy
Tools Used
- Okta workforce Identity
- AWS IAM Identity Center
- GitHub
- Microsoft 365
- Slack
What I learned
This project helped me understand how IAM Systems are designed beyond basic configuration. I learned how to separate roles from access, automate provisioning using attributes, and apply security controls like MFA based on risk level.
What I Would Improve Next
- Add Okta Workflows for lifecycle automation
- Implement access request approvals
- Add logging/monitoring integration



Leave a comment