This project demonstrates my hands-on experience with Identity and Access Management (IAM) in a hybrid environment using Active Directory and Microsoft Entra ID.
In this lab, I implemented user lifecycle management, role-based access control (RBAC), and least privilege principles to a fictitious company (Northwinds.com) to simulate real-world enterprise identity workflows.
Overview
This project focuses on building and managing a hybrid identity environment where Active Directory serves as the source of truth and Entra ID extends identity into the cloud.
Key Objectives:
- Manage user identities across on-prem and cloud environments
- Implement group-based access control (RBAC)
- Enforce least privilege for different user types
- Simulate real-world IAM provisioning workflows
Tools & Technologies:
- Active Directory Domain Services (AD DS)
- Microsoft Entra ID (Azure AD)
- Azure AD Connect
- Windows Server (VirtualBox)
- Role-Based Access Control (RBAC)
Architecture & Design
I designed a structured identity environment using:
- Organizational Units (OUs) for departments (HR, IT, Finance, Sales)
- Security groups for access control
- A global “All Employees” group fore baseline access
- A separate Contractor group for restricted users
This design supports scalability, centralized management, and least privilege enforcement.
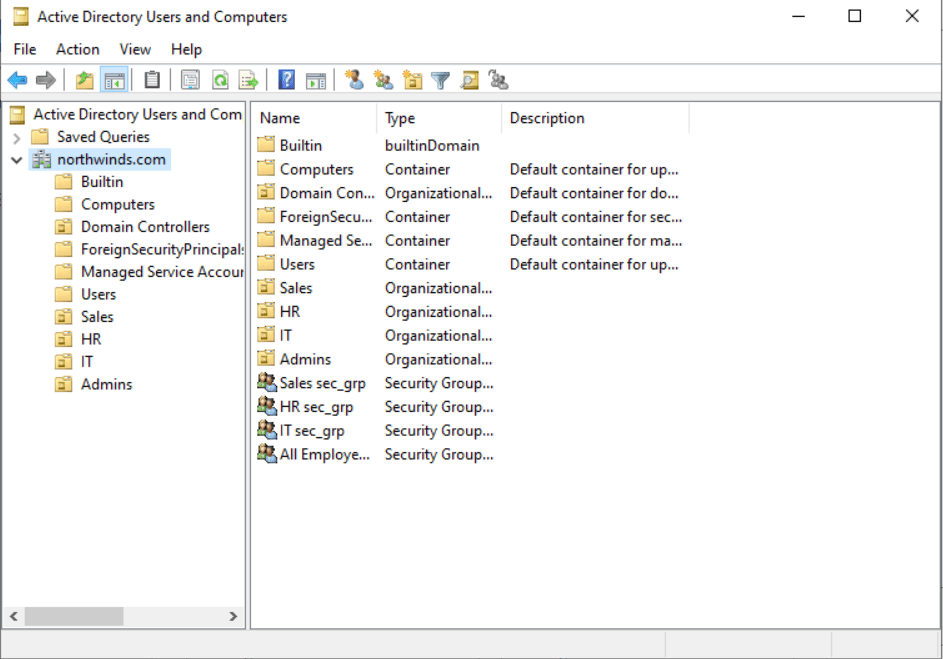
Figure 1: Active Directory Organizational Unit Structure
IAM Implementation
Identity Lifecycle Management
- Created and managed user accounts in Active Directory
- Placed users in appropriate OUs based on department
- Assigned group memberships based on role
- Synced identities to Entra ID
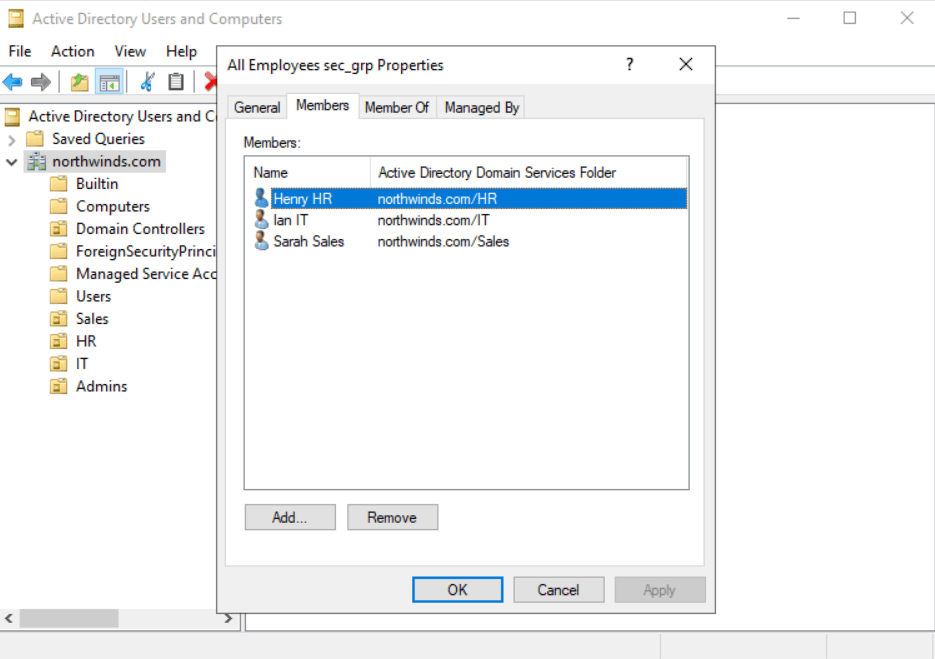
Figure 2 : User Management in Active Directory
Role-Based Access Control (RBAC)
- Implemented department based security groups
- Assigned users to groups instead of direct permissions
- Used “All Employees” group for baseline access
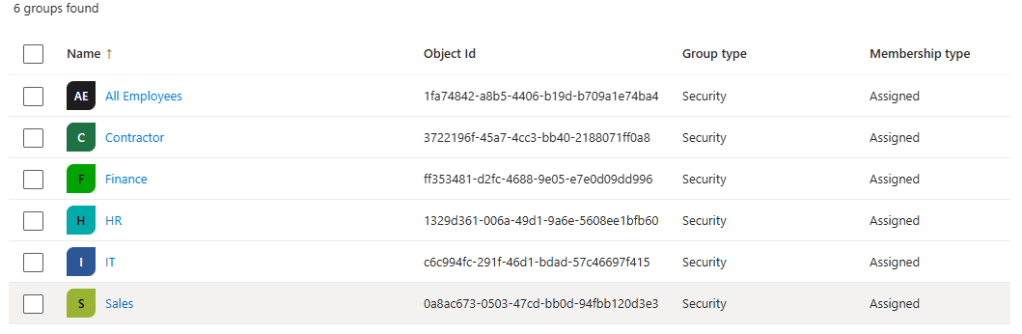
Figure 3: Group-Based Access Control in Entra ID
Hybrid Identity Integration
- Configured Azure AD Connect to sync identities
- Enabled authentication across on-prem and cloud systems
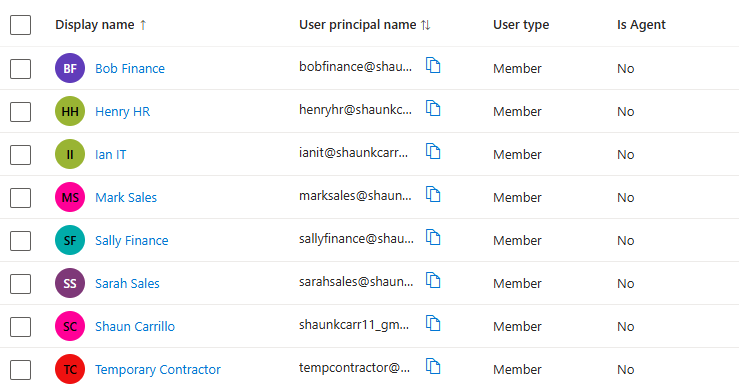
Figure 4: Synced Users in Entra ID
Ticket Scenario (Real World Simulation)
Business Requirement
Provision a new Finance department, onboard users, and create a restricted contractor account.
Actions taken
- Created Finance OU and security group in Active Directory
- Created corresponding group in Entra ID
- Onboarded:
- 2 Finance users
- 1 Sales user
- Assigned:
- Department-specific groups
- “All Employees” baseline access
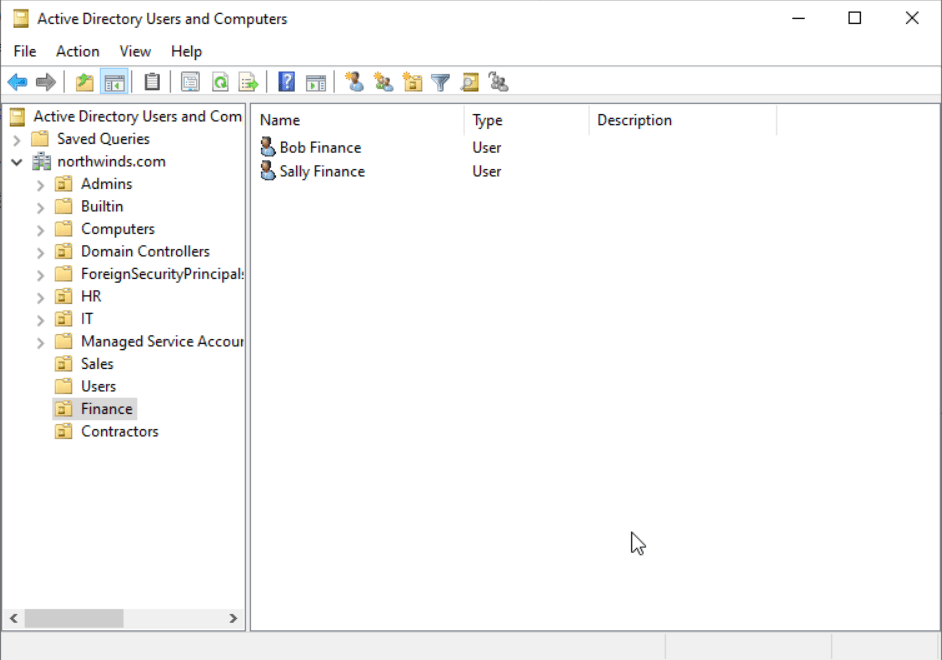
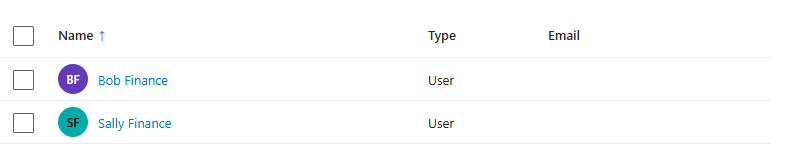
Figure 5: Finance Department Setup
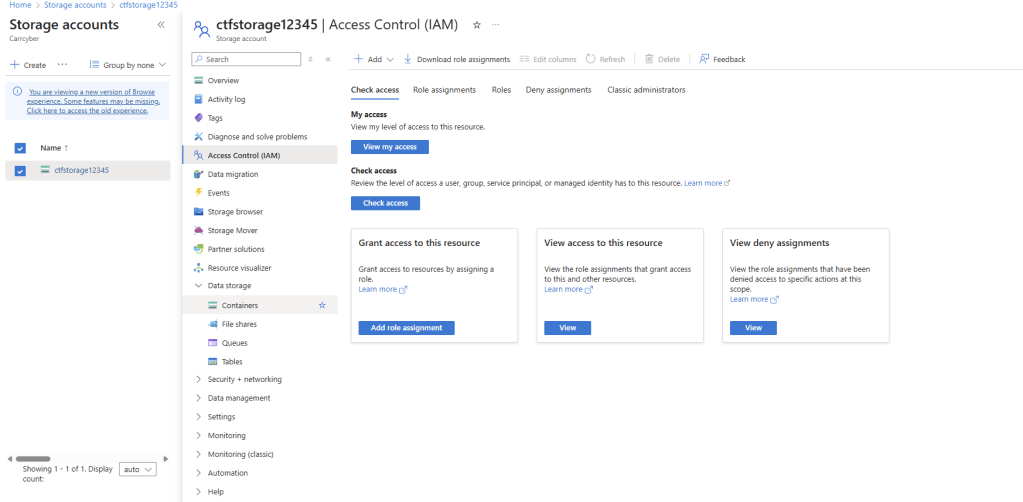
Contractor Access Control
- Created OU and security group
- Excluded contractor from “All Employees” group
- Enforced least privileged access
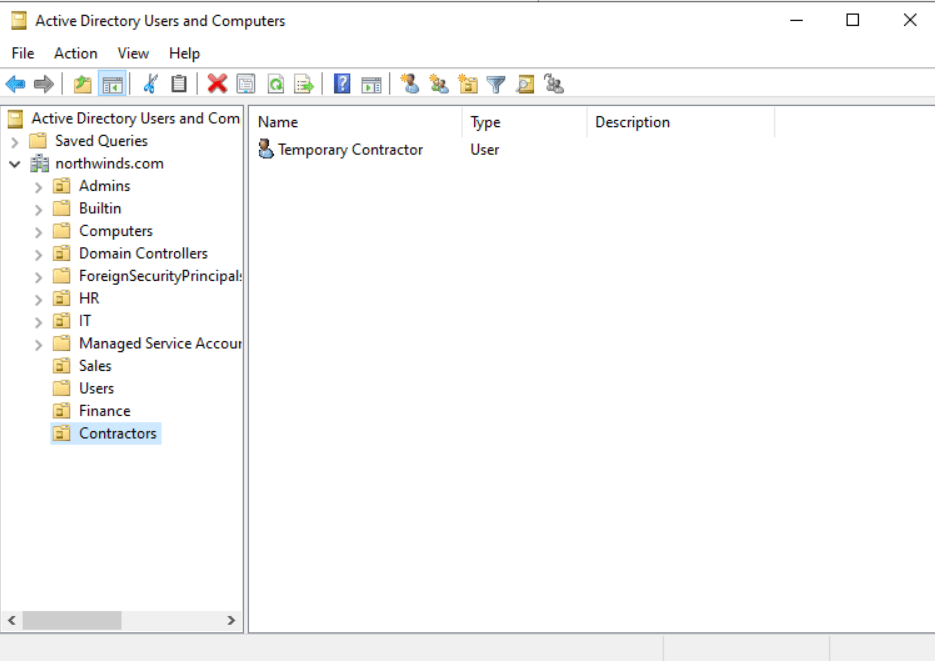
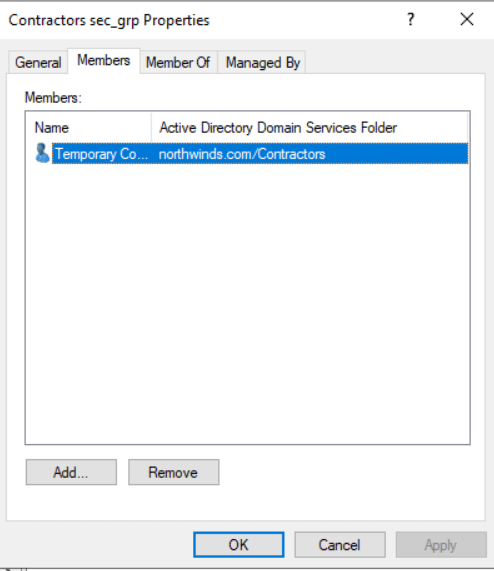
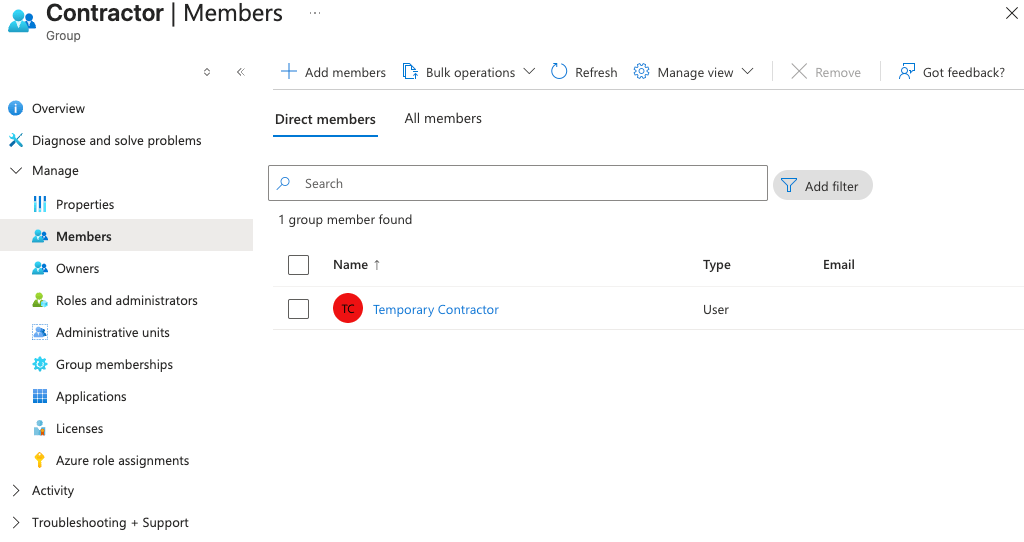
Figure 6-8: Restricted Contractor Access Model
Security & Access Control
- Enforced least privilege principles
- Segmented access between employees and contractors
- Reduced risk by limiting unnecessary permissions
- Used RBAC for scalable permission management
Skills Demonstrated
- Identity Lifecycle Managment
- Active Directory Administration
- Microsoft Entra ID (Azure AD)
- Role-Based Access Control (RBAC)
- Hybrid Identity (Azure AD Connect)
- User Provisioning & Access Control
- Least Privilege Enforcement
How this Applies to Real-World Roles
This project reflects real-world IAM responsibilities such as:
- User onboarding and offboarding
- Managing access through RBAC
- Maintaining identity consistency across systems
- Enforcing security best practices like least privilege
Final Takeaway
This project demonstrates my ability to design and manage a scalable hybrid IAM environment, aligning with enterprise practices for identity governance and access control.


Leave a comment